CSSCurrent en:Policy Conflict Solution
About Policy Conflict Solution
As Cryptshare considers all matching policy rules for a sender/recipient combination it might occur that multiple rules apply for a certain transfer and the settings of the matching rules differ from each other. For example there could be a rule that allows all users of your domain to send a maximum file size of 2 GB to anybody, and a second rule might explicitly define that one specific email address out of your email domain may send 5 GB to a certain business partner. This section gives administrators the possibility to configure how Cryptshare shall handle these conflicts.
Controls
List Components (Priority Order)
The list component will show a list of items that can be attached to policy rules (For example email signatures). If several policy rules match a sender/recipient combination and the setting is not the same for all matching rules, the matching list item with the highest priority will be used for the transfer.
Checkboxes regarding numeric values (Use maximum)
If several rules match a specific sender/recipient combination and the setting is not the same for all rules, the maximum value will be used if this checkbox has been enabled. Otherwise the minimum value will be used.
Checkboxes
If several rules match on a sender/recipient combination and the setting is not the same for all rules, the setting of the respective checkbox will be used for the transfer.
Dropdowns
If several rules match on a sender/recipient combination and the setting is not the same for all rules, the setting of the respective dropdown will be used for the transfer. All dropdown fields give the possibility to use the server setting that has been defined in the corresponding section of the Administration Interface. Please refer to the corresponding chapter of this administration manual for further information.
Advice on Conflict Solution
Password options
There are no specific settings available to influence how password-mode conflicts are resolved as this is done automatically. The most secure option of all applicable policy rules for a specific transfer is used. The security ranking is as follows (from high to low):
- Auto-generated password
- Manual password
- No password
Security modes
Available security modes
There are no special controls for resolving conflicts related to security modes. These conflicts are automatically resolved so that only those security modes that are allowed in all applicable rules are selected from all applicable rules for a transfer. If only an empty intersection of allowed security modes exists, the most accessible security mode is selected from the sum of all available security modes based on the following priority list and will be displayed to the user:
- Password
- QUICK
- ID Provider
Default security mode
There are no special controls for resolving conflicts related to the default security mode. These conflicts are automatically resolved by selecting the most accessible default security mode from all the rules applicable to a transfer based on the priority list above, which also appears in the list of available security modes. QUICK enabled when established There are no special controls for resolving conflicts related to the selection of QUICK as the default security mode, when a QUICK connection has been established. These conflicts are automatically resolved by setting this option if at least one rule applicable to a transfer has this option enabled and if the list of available security modes contains QUICK.
Handling internal transfers differently
If you want to handle internal transfers (i.e. transfers from one employees to another) differently than transfers between your employees and external contacts, you should consider the following: When automatically deriving policy rules from the licence key, two rules are created per licenced domain. These rules have the effect that
- all members of your domain can send to any recipient (position 1)
- any sender can send to members of your domain (position 2)
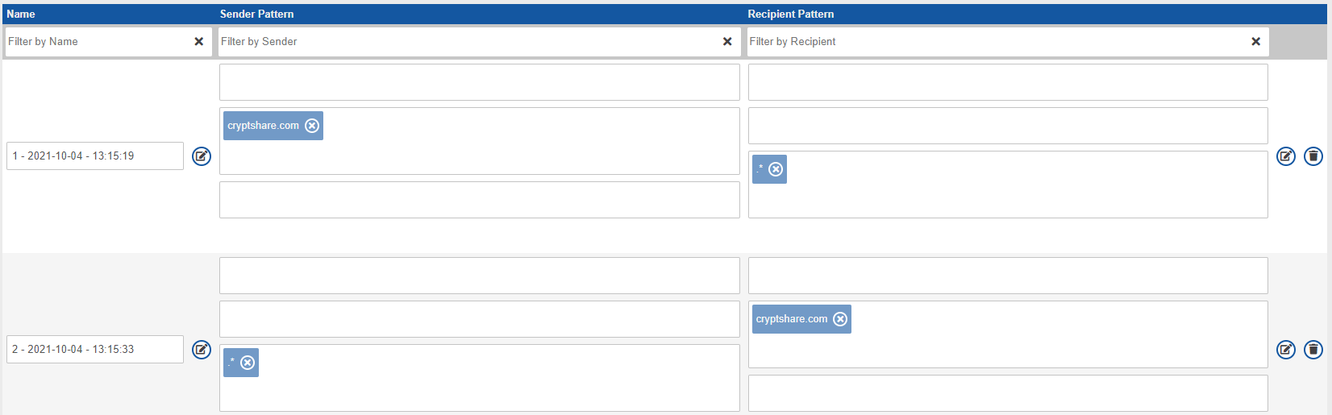 If you want to handle internal transfers with different policy settings, it is not sufficient to add a rule for this case (example: rule 3).
If you want to handle internal transfers with different policy settings, it is not sufficient to add a rule for this case (example: rule 3).
 You should also explicitly exclude your own email domain from the recipient definition of the outbound policy rule (rule 1) and from the sender definition of the inbound policy rule (rule 2). Otherwise an internal transfer would trigger all three policy rules and rule 3 would not explicitly apply. Instead, the transfer would be performed based on the results of the policy resolution evaluating all three rules which could lead to undesired results in some cases.
You should also explicitly exclude your own email domain from the recipient definition of the outbound policy rule (rule 1) and from the sender definition of the inbound policy rule (rule 2). Otherwise an internal transfer would trigger all three policy rules and rule 3 would not explicitly apply. Instead, the transfer would be performed based on the results of the policy resolution evaluating all three rules which could lead to undesired results in some cases.
When performing an internal transfer, you notice that passwords still have to be entered. Due to the logic of the three existing rules, all of the three rules apply when you send a transfer from a member of your domain to another member of your domain. The password settings of all three rules are evaluated and Cryptshare automatically chooses the most secure option out of these three rules, even though the transfer is internal.
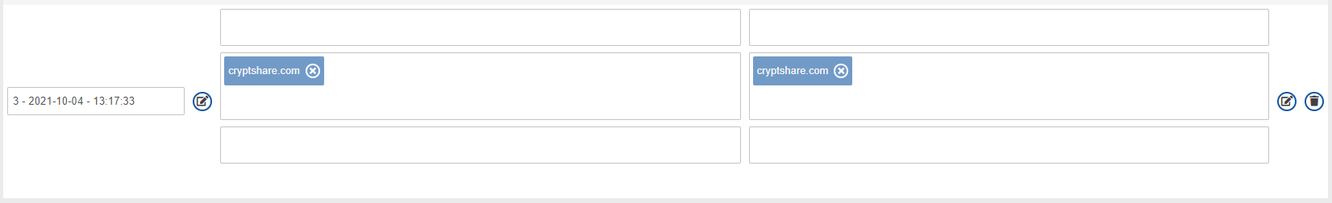
By excluding your domain from the recipient pattern in rule 1 and the sender pattern in rule 2, only rule 3 applies for internal transfers and not password entry is required.To change the inbound and outbound policy rule accordingly, please proceed as follows:
Edit the existing rules for inbound and outbound transfers (rule 1 and 2 in the example above) and change the sender pattern in rule 1 and the recipient pattern in rule 2 from `".*"` into `".*?@(?!yourdomain\.com).*"`
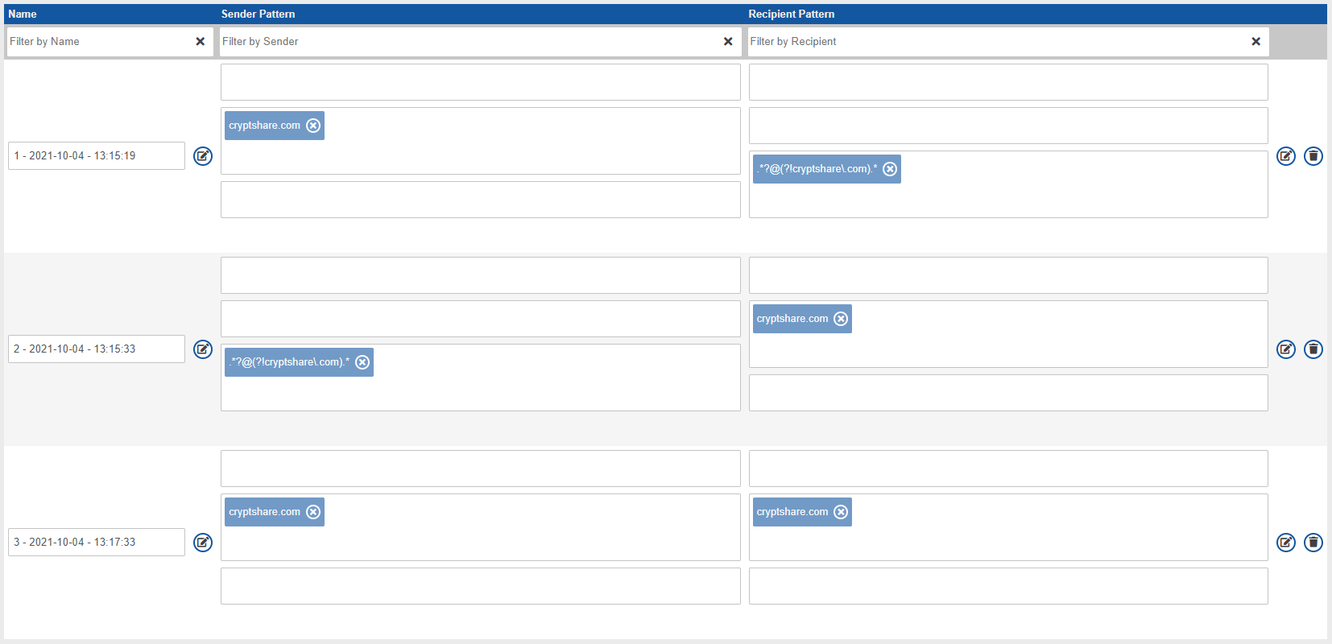 In the example shown, rule 3 is now the only rule which applies when sending transfers from cryptshare.com to cryptshare.com so its settings will apply exclusively.
In the example shown, rule 3 is now the only rule which applies when sending transfers from cryptshare.com to cryptshare.com so its settings will apply exclusively.